Sign-in Scenarios: Counter vs. Self-Service
Nowadays, computer labs in academic institutions employ two major methods of user sign-in. These are "Counter sign-in", when Lab Assistants assign incoming users to workstations, and "Self-Service sign-in", when users log in using account credentials stored in an enterprise directory such as LDAP or MS Active Directory. Both methods exist in a variety of flavors. How VeraLab adds value in each scenario?
Here we will explain how VeraLab supports these scenarios
- Counter Sign-In
- Self-Service Sign-In
- How VeraLab Supports Self-Service Sign-On Scenario
- How VeraLab Supports Counter Sign-In Scenario
- Common Capabilities
- Intranet Capabilities
- Conclusion
-
Counter Sign-In
Every incoming user signs in to a workstation through a Lab Assistant who is responsible for assigning users to computers in a computer room. The Lab Assistant verifies the userÂ’s identification. The degree of automation may vary. Some institutions maintain a paper log where students are recorded. Others deploy a sign-in application that keeps access logs in a digital form. Those who are most computer savvy deploy a Lab Management System with advanced security, access control, and surveillance capabilities.
-
Self-Service Sign-In
Every user has an account created in a central directory. Registered users who come to a lab are free to choose any available workstation and log in using their account credentials. Lab personnel provide technical or customer support rather than access control.
-
How VeraLab Supports Self-Service Sign-On Scenario
Each workstation in the lab is equipped with VeraLab Guard, the module that performs the monitoring the workstation log-in state. Once a user logs in (presumably using directory authentication), VeraLab Guard sends a log-in notification to VeraLab Server. VeraLab Server validates the user against Alert List and checks whether the workstation is available for user sign-in. In case the Alert List prohibits the user from signing-in or the workstation has been marked as unavailable for sign-in, VeraLab Server responds to VeraLab Guard with logout response. As a result VeraLab Guard logs the user out.
Once the user logs out, VeraLab Guard sends a logout notification to the VeraLab Server, and the VeraLab Server records the end of the user session.
Lab Assistants can periodically view the status of the lab through the "Monitor" module. This module will show them the current status for each workstation including user names of signed-in users, Alert List notifications, workstation occupancy, and availability.
Figure 1. Screenshot of a "Monitoring" module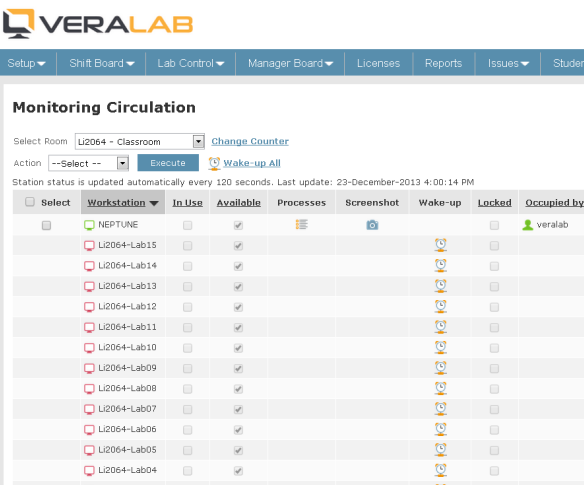
-
How VeraLab Supports Counter Sign-In Scenario
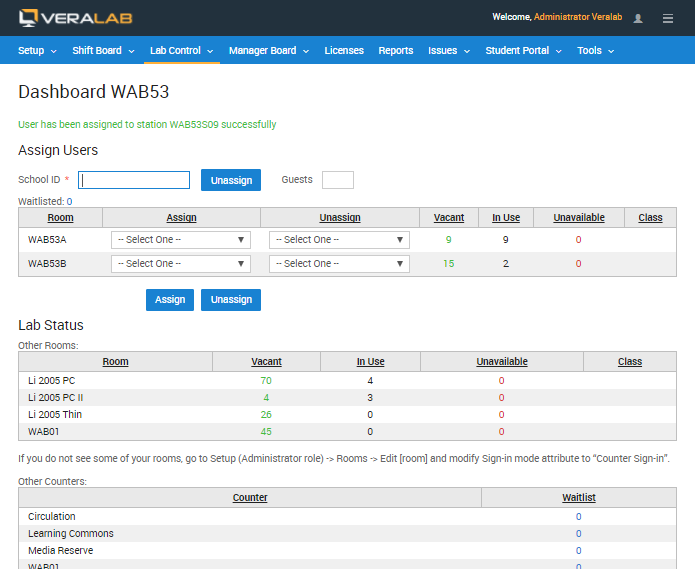
VeraLab provides Lab Assistants with a "Dashboard" module that supports the following front-end activities:
Figure 2. Screenshot of Lab Assistant Dashboard
- Assigning users to workstations. Data from the user ID card are scanned and saved to the access log database. Users can be assigned to and unassigned from workstations. Unattended workstations can be locked to prevent unauthorized access. Locking/unlocking can be integrated with user sign-in.
- Viewing computer room status. The Lab Assistant can view the occupancy of multiple computer rooms and can redirect incoming users from over-occupied to under-occupied rooms.
- Alert List notifications. To prevent abusers from accessing a computer facility, the Lab Assistant will be notified if the incoming user has been added to the Alert List.
- Class registration. To prevent public access while a class is being performed, the Lab Assistant can mark the room as occupied for the class.
-
Common Capabilities
Besides user sign-in, VeraLab provides the following value-added capabilities equally useful in both scenarios:
Front-End
Surveillance and Remote ControlIn both scenarios, Lab Assistants have access to the "Monitor" module, which provides a powerful set of surveillance and remote control capabilities aimed to prevent users from performing unwanted activities and stop these activities once they occur. These include capturing user screenshots, sending messages to one or multiple workstations, viewing a list of currently run processes, terminating remote processes, preventing launch of particular software packages, preventing launch of software from removable media, forcing user logout, and computer shutdown.
Figure 3. Screenshot of user workstationSoftware Metering and Concurrent License Management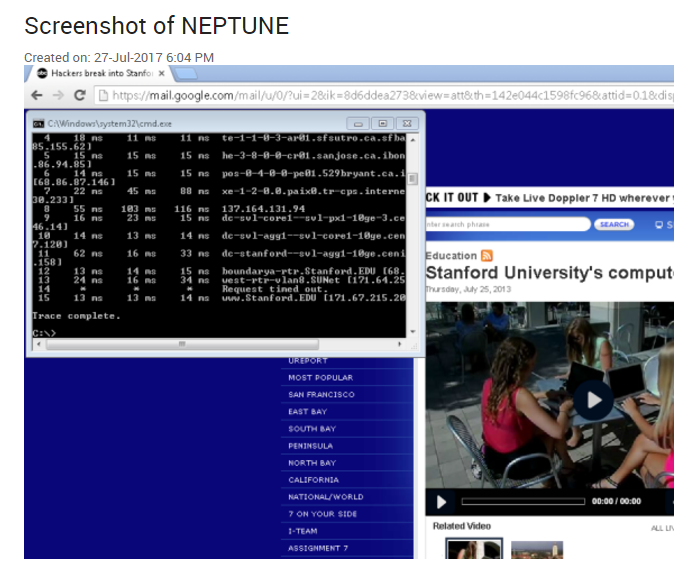
In both modes VeraLab can limit the number of simultaneously used instances of a software product. This allows a lab to purchase only a few concurrent licenses of a pricey software package, install it on all the workstations in the lab, and ensure that the number of concurrently used instances does not exceed the number of concurrent licenses. This solution provides cost savings (fewer licenses to be purchased), user satisfaction (the software is available on every workstation; no more waitlists), and ease of maintenance (only one disk image is needed for the entire lab).
Figure 4. Screenshot of software metering dashboard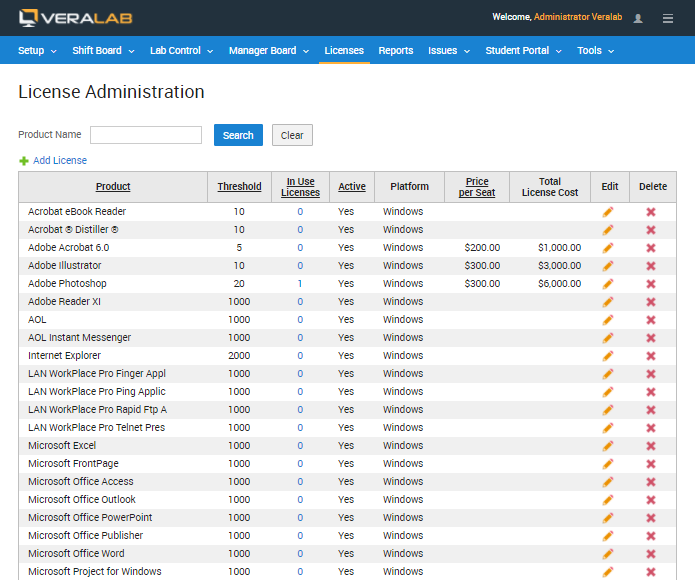
Back-End
Access Log Analysis and Alert List ManagementThe access log can be analyzed to identify potential abusers. Abusers, identified during access log analysis, can be added to the Alert List to control/prevent their access to the computer resources in the future. To learn more about lab security, please read the "Establishing a Secure Lab Environment" whitepaper.
Maintenance AutomationThe Issue Tracking database allows Lab Assistants to enter maintenance issues, and Technicians to handle these issues in an orderly fashion. Collaboration between Lab Assistants and Technicians is streamlined and does not rely on sticky notes and flip-over signs anymore. Technicians can mark workstations unavailable for sign-in, which will automatically prevent user sign-in in all sign-in modes.
Supervisory ActivitiesLab Coordinators can view current status of the lab from any place on the Internet. Lab Assistant attendance data can be collected in any form convenient for presentation to HR and Payroll services.
Managerial Decision SupportUser sign-in and maintenance data can be pulled into tabular and graphical reports invaluable for making scheduling, budgeting, staffing, purchasing, and other managerial decisions. To learn more about VeraLab features, please read the "Build a Secure and Efficient Computer Lab Through Lab Management System" whitepaper.
-
Intranet Capabilities
Many academic institutions develop Lab Information Portals where users can view lab schedules and locations, and find workstations equipped with a particular software package. This is a must in a self-service scenario when Lab Assistants are not always available. Often current lab occupancy and workstation/software availability data are not available, which presents a major customer satisfaction issue. Real-time user sign-in data stored in the VeraLab database can be requested by the portal so that users can find answers 'to the following questions:
- What rooms have workstations available now?
- Is the software I need available now?
VeraLab Inc. plans to develop VeraLab Info Portal, the out-of-the-box user information system ready to be plugged into your Intranet. The system will feature deeper functionality than the ones developed in-house by leading academic institutions. If you are interested in contributing to product requirements, or participating in our beta testing program, please contact us at info@veralab.com.
-
Conclusion
VeraLab can easily be configured to support both Counter and Self-Service sign-in scenarios. In both scenarios VeraLab provides a considerable added value in areas of security, operational management, and customer satisfaction.
VeraLab Inc. is an innovative software company located in Silicon Valley, CA. Our core business is Computer Lab Management Systems. Our flagship product is VeraLab, a comprehensive lab management suite targeted for academic institutions and corporate training centers. To find out more about VeraLab, please visit VeraLab Home Page.




